
Ahmedajaz | Identity & Cloud Security
Entra ID, IAM Governance & Cloud Security Automation

Entra ID, IAM Governance & Cloud Security Automation
The Zero Trust security model has become the cornerstone of modern cybersecurity, and identity lies at its heart. This article explores how to implement a Zero Trust strategy for Identity Security by combining adaptive access controls, continuous validation, and automation-driven governance.

Zero Trust is not a product, it's a mindset. The principle “Never trust, always verify” means every access request, user, or device must be continuously validated. In identity-centric security, this translates to enforcing strong authentication, contextual access, and least-privilege permissions.
With cloud adoption and remote work, traditional network boundaries have dissolved. Identities - users, devices, and services - now define access boundaries. Platforms like Microsoft Entra ID, Okta, and Ping Identity enable conditional access, continuous access evaluation, and adaptive MFA to enforce Zero Trust principles.
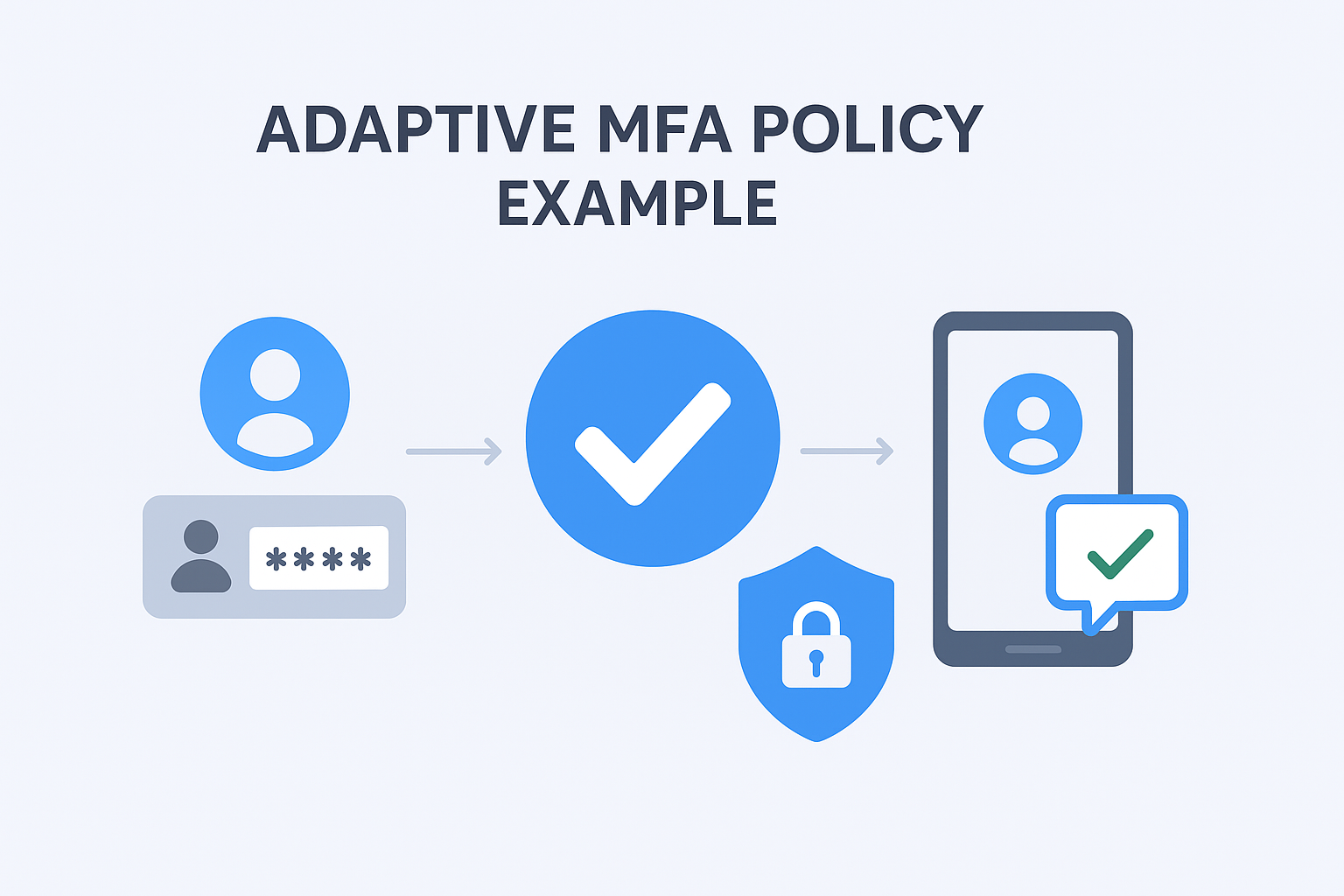
Start by assessing your current identity posture, how access is provisioned, governed, and monitored. Introduce adaptive conditional access, enforce MFA, and integrate your PAM system with your IdP. Finally, automate review cycles and apply analytics to continuously evaluate risk signals.
A Zero Trust Identity strategy is not just a security upgrade, it’s an operational transformation. By continuously verifying trust and automating governance, organizations can build a resilient foundation for secure digital innovation.